At Shorsec, we assess your cyber assets to discover vulnerabilities. We help secure your cyber landscape, so you can safeguard your organization and protect your data.
View ServicesAs technology constantly evolves, so does the hackers tactics.
You need to defend your networks and get ahead of malicious actors - before they manage to access your private data.
Discover where, how and why vulnerabilities occur. Learn how to safeguard your organization and protect your data.
Evaluate the effectiveness of your security measures and identify your level of risk against sophisticated adversaries.
Assess your web applications, networks, systems, and wifi to pinpoint the vulnerabilities that put your organization at risk.
Analyze your existing security measures, determine your level of risk and bring your organization’s security posture to a higher level.
Our team of professional cybersecurity experts will assess, evaluate, and penetrate your network to ensure your data is safe from all angles.

At ShorSec, our goal is to identify your unique security priorities and strengthen your security posture.
By identifying your most critical assets, we can effectively pinpoint the weaknesses in your security controls that affect you most. Our team of experts utilize the latest adversary tactics and techniques to assess the effectiveness of your security measures and help your secure your organization.
Manage your risks and know that you’re protected against attacks.
Get in TouchAny cybersecurity consultant can try to penetrate your network. It’s how you interpret the results that count. At ShorSec, we are experts at detecting the loopholes and analyzing the findings, so you can close them down before the hackers have a chance to abuse them.
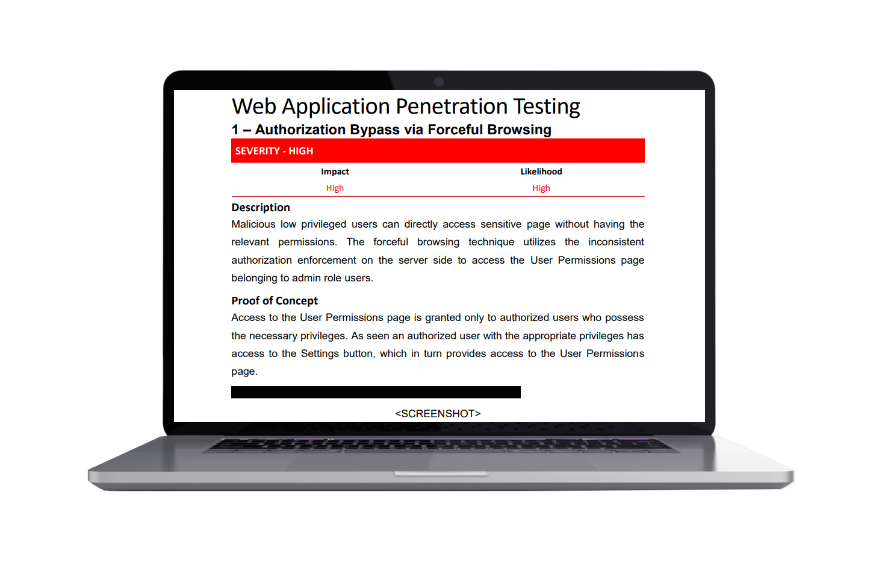
Get a comprehensive view of your security posture. Identify and remediate vulnerabilities before they can be exploited by malicious actors.

New “threadless” process injection technique that works by utilizing the concept of DLL Notification Callbacks in local and remote processes.
Learn cutting-edge offensive techniques and improve your tradecraft as a cyber security professional.
Network Administration & Cyber-Security
Penetration Testing
Advanced Web Application
Penetration Testing
Advanced Red
Teaming
Introduction To
Malware Development
Advanced Malware
Development
Assumed Breach
Operations
At ShorSec, we are on a mission to help you secure your cyber landscape
We’re sharing our tools openly with the community – so you can strengthen your networks and keep your data private and protected.
Enter your email address to receive cyber security tips, techniques, and updates

Email: contact@shorsec.io
Phone: +972 50 270 0888
powered by nextbracket.io